While you only need one key to lock your apartment door, the digital world is far more complicated. People often have dozens of accounts online – and just as many passwords to protect them with. Since building a password that is equal parts unique and secure can be frustrating, we have prepared some ideas and suggestions for strong passwords to keep you one step ahead of hackers.
What is a good password?
You might think that the answer to this question would be very subjective, but that’s far from the case. In simplest terms, a good password is one that’s difficult to crack. The stronger your password is, the better it works to protect your accounts from hackers and other malicious actors. A strong, reliable password can sometimes take millions of years to crack, which means that the hackers are less likely to even try to gain them.
When you’re thinking of good password ideas, you need to keep the following criteria in mind:
The password should be at least 12-15 characters long.
It should use a combination of letters, numbers, and special characters. Spaces are also allowed.
It should not be a common word, product, character, name, or anything you can easily find in a dictionary.
It should be a combination that only you know and others could not easily predict. We’ll cover some creative password ideas shortly.
Each password should be unique and you shouldn’t reuse them for several accounts. If a password you use on several platforms is cracked, that puts all of your accounts at risk.
What is considered a weak password?
Weak passwords consist of sequential letters or numbers, are fewer than eight characters long, or use common words and phrases. The most popular passwords are well-known by malicious actors and are usually what they try first.
According to NordPass’ annual top 200 most common passwords list, “123456” and “password” are the most commonly used and vulnerable passwords. Another example of a weak password would be using the name of a fictional character like “Superman,” “Batman,” or “Joker.”
Examples of bad passwords
Here are some more examples of weak, easy-to-crack passwords:
123456789
abc123
qwerty
iloveyou
hello
computer
password123
If you’re wondering whether your passwords might be weak links, check out the list of the top 200 most common passwords. You’ll find even more examples, as well as some fun facts about the most common passwords around the world.
The most common password-cracking techniques
Brute-force attack
During a brute-force attack, a malicious actor uses software that tries every possible combination to find the right one. An eight-character password consisting of upper- and lowercase letters, numbers, and special characters can be cracked in just two hours. Good passwords will take months or even years to break through, depending on their uniqueness and complexity.
Dictionary attack
While brute-force attacks try various combinations of special characters, numbers, and letters, a dictionary attack uses a program that goes through a prearranged list of words. Essentially, if your password can be found in a dictionary, specialized software can easily crack it.
Phishing
Phishing is a social engineering method to trick people into revealing their credentials. Phishing attacks often use email services as a medium: hackers send emails pretending to be reputable sources and refer users to fake login pages. A user then inputs their login credentials themselves and inadvertently grants this information to the hackers.
Credential stuffing
Credential stuffing is a popular method for hackers to gain access by collecting usernames and passwords used in previous attacks and trying them on other platforms. This method often proves successful because people tend to reuse the same password for all their accounts.
Keylogging
Keylogging involves a specific type of malware, known as keylogger, infecting the victim’s device. The keylogger can then track the user’s keystrokes and device activity, depending on the software and the device. This can include copied and pasted data, phone calls, location, and screenshots. Using this information, hackers can easily access passwords and other sensitive information, allowing them to launch further attacks on the individual or data from their place of work.
How to create a strong password
The longer your password is, the better. Many websites ask you to create eight-character passwords, but we recommend going for at least 15 characters.
Avoid ties to your personal information, such as your name, surname, address, or date of birth.
Use a combination of numbers, symbols, and upper- and lowercase letters in random order.
Don’t use sequential letters and numbers.
Avoid substitution: “kangaroo” and “k@ng@r00” are both equally weak passwords, and a brute-force attack can easily crack them.
Don’t reuse the same password for multiple accounts.
With our free password security tool, you can check your password strength and if it has been exposed in any data breaches. You can also try the Password Health feature with NordPass Premium. It scans all passwords that you’ve saved in your Vault and checks for vulnerabilities.
Top 5 strong password ideas
Coming up with a strong and unique password can be a challenge. To make this process easier for you, we’ve gathered some examples that will help protect your data and accounts from being breached and taken over. We’ve also included some formulas and passphrase examples that you can try yourself. However, we highly recommend you don’t use the example passwords for your accounts.
1. Shorten each word
Think of a phrase and remove the first three letters of each word (in some cases, that might mean deleting full words, but that’s fine):
“Laptop running free in the jungle” -> “top ning e gle”
Sounds like gibberish? That’s exactly what we want. Just don’t forget to add special characters and numbers to make it more complicated. It would take 94,000 years to crack this password.
2. Create your own formula
Create a formula that will help you remember the password. For example, you can take a phrase and replace every letter with the next one in the alphabet:
“Cucumbers are tasty” -> “dvdvncfst bsf ubtuz”
Another clever way of creating strong passwords is to turn song lyrics into acronyms. This means using only the first letter of each line of your favorite song.
So, “Shine on you crazy diamond” by Pink Floyd becomes “rsnsybccystswrcc.”
The time needed to crack this password is 746 million years.
3. Play with the vowels
This one is much easier to implement and memorize: take a random nonsensical phrase and replace one vowel with another (for example, “a” with “e”):
“A car is floating in a pan” -> “e cer is floeting in e pen”
Don’t forget – spaces are allowed in passwords, and we highly encourage you to use them. The combination of having spaces and switching the vowels around means the above password would take 583 million trillion years to crack.
4. Mix the codes of your favorite countries
This one is quite fun and easy to memorize. You will always generate good passwords with this method. Simply make a list of the ISO codes of your favorite countries and put them together:
“Mexico, Ireland, France, Germany, Japan” -> “mex irl fra deu jpn”
You wouldn’t think so, but a hacker would require a staggering six thousand trillion years to crack this password!
If you want to spice things up and make them even more difficult to crack, you can also add each country’s calling code:
“mex54 irl353 fra33 deu49 jpn81”
Such a password would take 12 decillion years years to crack. How impressive is that?
5. Use a password manager
If creating and remembering random phrases for all your accounts seems too complicated, you can use a password manager, such as NordPass. It’s an easy-to-use app that lets you generate strong, unique passwords and securely store them in an encrypted Vault. You can also easily use NordPass to autofill online forms and fields.
You can add as many passwords as you need and access them from any device. This way, you can get the best of both worlds by combining your creative password ideas with one-of-a-kind secure ones created by the password manager for each account without the risk of forgetting them. You can use a special code and get an additional month of NordPass Premium for free when you purchase a two-year plan.
Additional tips
Here are some more tips to keep in mind when you’re looking for good password ideas:
In order to protect your data, remember that passwords must be difficult to predict. Including special characters and spaces increases the time it takes for your password to be cracked.
Take your phone security into consideration. According to research, pattern locks are successfully replicated around 64% of the time. Instead, set up a PIN or use our guide to generate some strong phone password ideas.
Don’t forget to implement new password ideas for work. Don’t reuse your personal passwords because if they ever get breached, your work accounts could be in danger, too.
Always use multi-factor authentication (MFA). Even if your password is definitively strong, accidents can happen and your first line of defense might be breached. Using MFA means that no one can access your accounts without accessing your authentication device. NordPass uses multi-factor authentication to add an additional layer of security to your password vault.
About Version 2 Limited
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
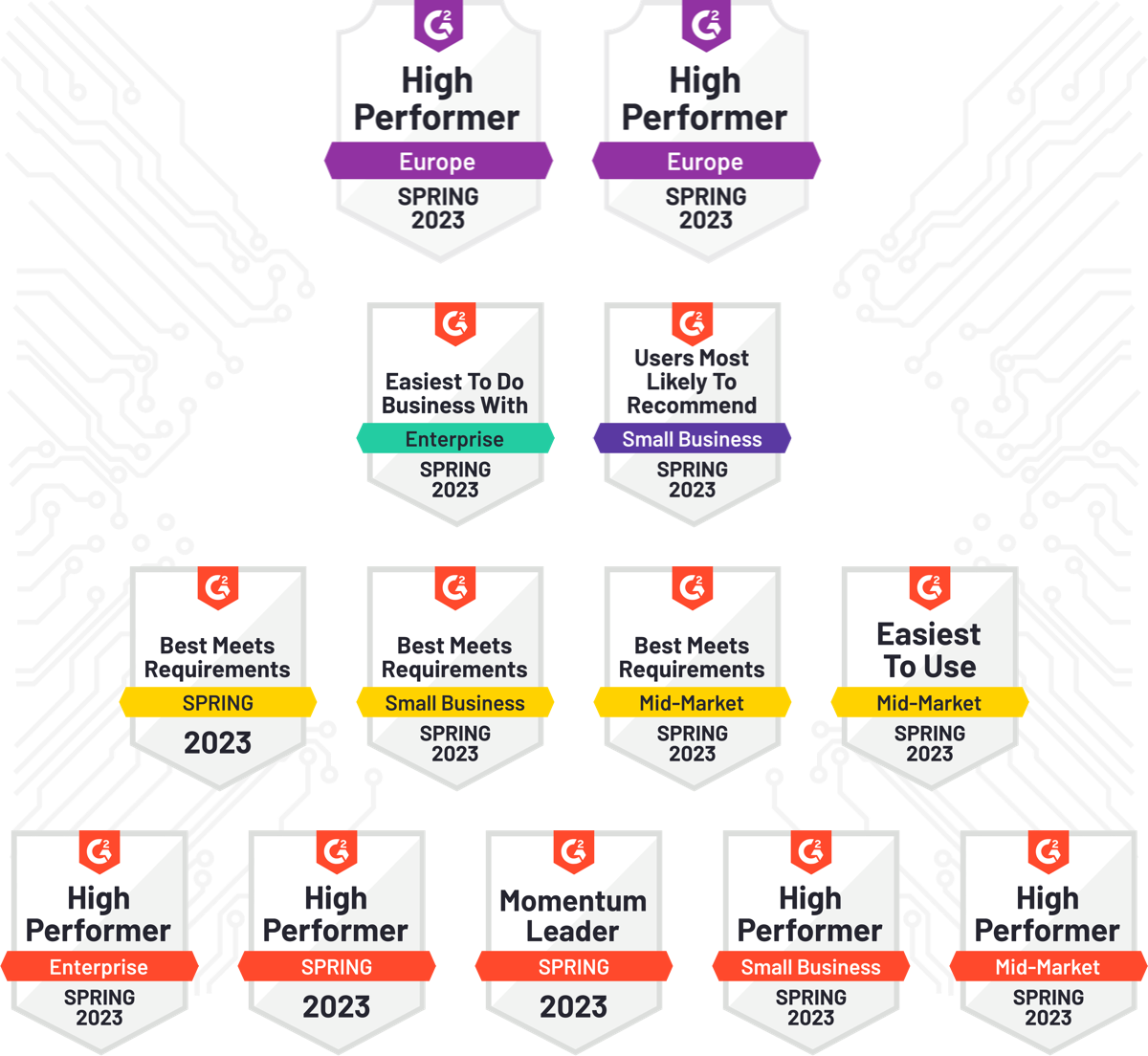
About NordPass
NordPass is developed by Nord Security, a company leading the global market of cybersecurity products.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.