Summary: Secure your supply chain by identifying threats, assessing vendor risks, and using NordStellar to manage vulnerabilities before they affect your business.
Cooperation is unavoidable in a complex economy where businesses depend on other companies to deliver services and products. However, working with third parties also introduces supply chain security risks.
Protecting the supply chain is a critical task for all organizations. The challenge encompasses tech suppliers, shipping solutions, logistics partners – and more. This guide will help you reduce cyber exposure with practical supply chain security solutions.
What is supply chain security?
Supply chain security manages risks related to suppliers, vendors, transportation, and logistics partners. It assesses external factors and recommends ways to reduce physical and cyber risks.
Supply chains differ by company and product line – there’s no one-size-fits-all approach. Instead, companies should apply defense-in-depth and robust supplier analysis to create tailored solutions for every situation.
Why is supply chain security important?
Supply chain security matters because external partners often represent a significant cybersecurity risk. Insecure supply chains expose companies to cyber threats like data breaches, ransomware, and DDoS attacks.
Supply chain vulnerabilities at a single vendor cascade to multiple clients, leading to many harmful outcomes. For instance, a compromised or malicious supplier exposes your business to:
- Supply disruptions – Attacks on vendors disrupt supply chains, interrupting digital services or the flow of physical components. Clients may need to scale down operations, hitting their revenue streams.
- Resilience and continuity issues – Supply chain attacks compromise clients’ ability to respond quickly and protect critical data. Attacks steal information, obstruct supply, take down systems, and create confusion. Restoring normal operations is difficult when threats originate outside the organization.
- Cyber threats – External partners become vectors for ransomware or data theft attacks. Attackers exploit security vulnerabilities at vendors. If vendors have privileged network access, attackers can leverage their position to access confidential data and critical systems.
- Reputational damage – Supply chain attacks often lead to data breaches at clients. For example, cloud vendors may expose client data to external threat actors. Data leaks erode trust and lead to reputational harm.
- Compliance pressure – Clients are responsible for securing customers’ data. Suppliers play a secondary role, but regulators hold data controllers responsible. As a result, supply chain security failures regularly lead to compliance penalties for clients.
These risks can have devastating consequences. For example, the 2021 Kaseya Attack affected 1,500 companies and demanded ransoms of $70 million. In that case, attackers exploited weaknesses in Kaseya’s remote monitoring tools to access client networks.
Common vulnerabilities in the supply chain
Kaseya is one example of how supply chain attacks work. However, criminals can target supply chains in many ways.
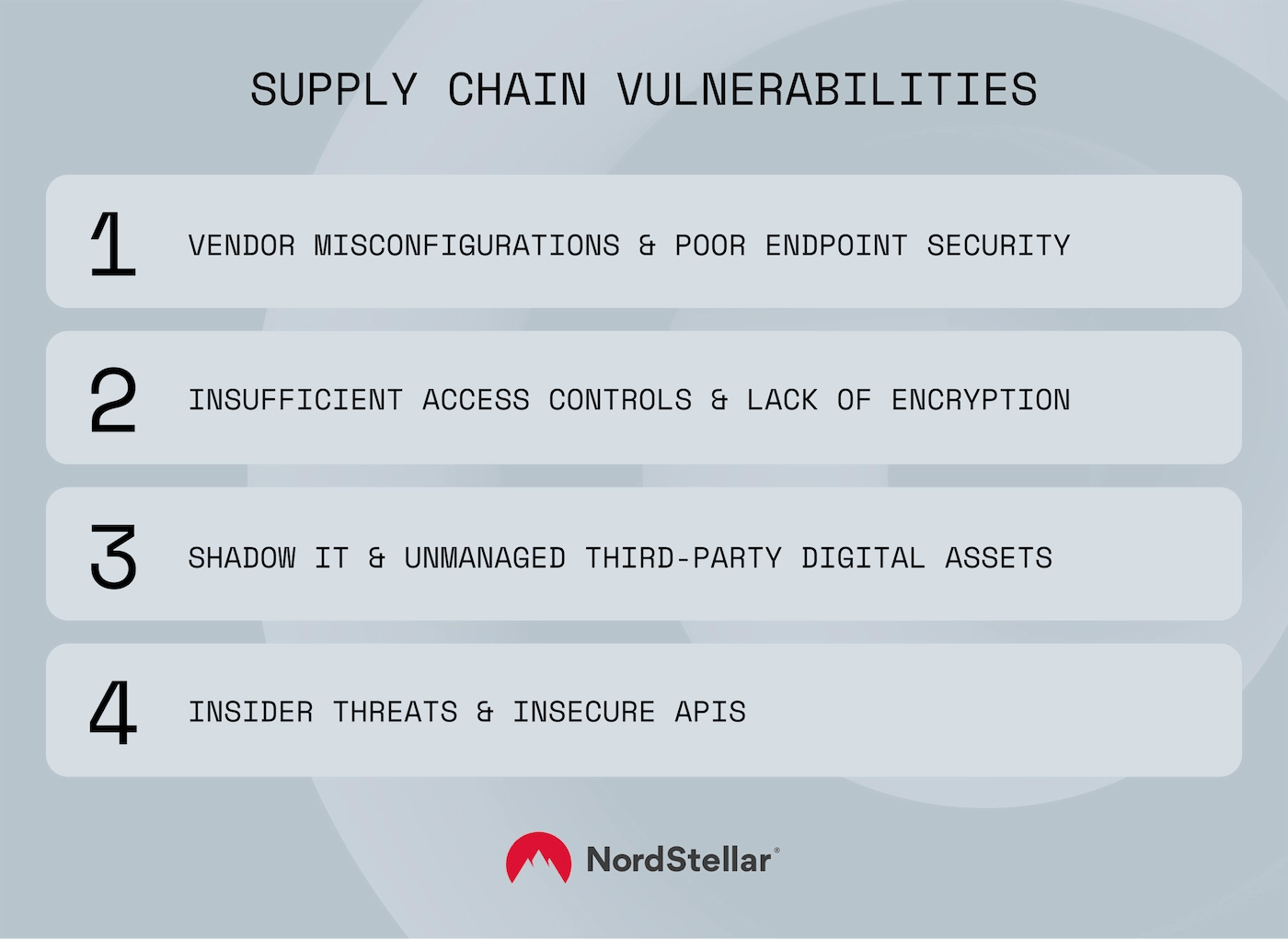
Companies must understand common supply chain security vulnerabilities when crafting effective security strategies. Common weak links in the chain include:
1. Vendor misconfigurations and poor endpoint security
Weak endpoint security and misconfigurations create vulnerabilities. For instance, cloud providers may leave ports unsecured or rely on outdated Endpoint Detection and Response (EDR) and antivirus tools.
This creates problems for clients. Attackers gaining access to the vendor network can propagate malware across hundreds of clients in a “cascade” effect.
The Solar Winds attack is a great example. In that case, attackers compromised Solar Winds’ Orion platform and used it to send malicious software updates. Clients applied the updates, assuming they came from a trusted source.
2. Insufficient access controls and lack of encryption
Attackers infiltrate vendor systems via credential attacks and weak access controls. Vendors should only allow access to authorized users who have legitimate business reasons. However, this falls apart if criminals can force access via credential-stuffing attacks.
Without robust access controls, attackers can breach the network edge and move laterally to access sensitive assets. Lack of encryption makes this situation worse by exposing data to enabling credential interception attacks.
3. Shadow IT and unmanaged third-party digital assets
Clients should control how suppliers use and access their networks. However, Shadow IT creates insecure endpoints and bypasses security management systems.
For example, suppliers could use external devices to maintain physical infrastructure or add cloud tools to their services without client consent.
Unmanaged assets create additional security risks. Clients may lack visibility of vendor products or security systems underlying cloud services. This creates space for malicious outsiders to breach client networks and delays incident responses as targets scramble to assess the threat.
4. Insider threats and insecure APIs
Integrated APIs as part of their services can become security vulnerabilities if vendors fall behind on patch management. As APIs often connect to multiple assets, this creates an internal cascade, affecting many systems within targeted organizations.
Insider supply chain risks are also critical. In some cases, vendors may unknowingly hire individuals with malicious intent. More commonly, suppliers act negligently or fail to follow security policies.
Threat types targeting supply chains
Understanding attack types is crucial to identifying threats and mitigating supply chain security issues. The table below summarizes the most common threat types:
Threat type | How it works |
|---|---|
Embedded malware | Attackers embed malware within legitimate hosts – for example, compromised DevOps components or software updates. |
Man-in-the-Middle (MiTM) attacks | MiTM agents intercept data flows between vendors and clients, enabling data theft or code injection. Attackers can use MiTM techniques to hijack update servers or control third-party libraries. |
Hardware tampering | This physical security threat alters devices before they reach clients. Criminals may add surveillance chips, or modify firmware to add backdoor access. |
Credential theft from third parties | Criminals steal vendor credentials and use them to access client networks. |
Data theft via insecure APIs | Attackers identify outdated or weakly secured vendor APIs. They use them to steal credentials and obtain access to linked network assets. |
CI/CD pipeline compromises | Attackers exploit the development pipelines used when testing and deploying software. This allows them to inject malicious code and bypass security measures. |
Social engineering attacks against vendors | Criminals obtain credentials via persuasive emails or phone calls and use these credentials to access client networks. |
Best practices to secure your supply chain
Given the threats and vulnerabilities discussed above, creating a secure supply chain is vital. But what tools can businesses use to mitigate supply chain risks?
It’s important to remember that vendors and clients share cybersecurity responsibilities. The core challenge for clients is building a secure supply chain framework. Here are some ways to do so:
- Conduct proactive third-party risk assessments for all suppliers, assessing their security practices, certifications, and compliance records.
- Adopt Zero Trust security practices within your network. Minimize vendor privileges and use network segmentation to limit access to unrelated assets. Verify users and devices via robust access controls before granting access.
- Operate a Software Bill of Materials (SBOM) for all digital products. SBOMs trace components, vulnerabilities, and dependencies – providing a template for risk assessment and incident responses.
- Implement real-time vulnerability management. Track supplier activity to detect suspicious behavior (such as unusual access requests or data transfers). Use automated alerts to trigger security measures before attacks escalate.
- Consider cyber insurance to help manage shared risk and mitigate financial fallout from third-party breaches. Cyber insurance recognizes that vendors and clients share responsibility to protect data, covering breach-related costs like legal fees and regulatory fines.
How to evaluate and monitor suppliers
Assessing suppliers is a critical cybersecurity challenge. Failing to audit vendors is a serious compliance violation under GDPR, HIPAA, and other data security regulations.
Organizations need a systematic evaluation approach to cover security fundamentals. For instance, your vendor assessment framework should:
- Verify the vendor’s security credentials – Request relevant certifications (such as ISO/IEC 27001 or SOC 2 compliance) during onboarding. Support certifications with audits to ensure vendors meet your security expectations.
- Enforce robust Service Level Agreements (SLAs) – Define the responsibilities of vendors and clients. State maximum response times for security alerts and agree upon breach notification procedures.
- Automate vendor risk management (VRM) – VRM tools continuously monitor vendor performance and highlight potential issues. They can also streamline vendor assessments by collating certifications and vendor questionnaires.
- Schedule training for suppliers – When onboarding, ensure vendors understand your baseline security best practices and expectations. Reinforce those messages with online testing, video conferences, and regular communication.
About NordStellar
NordStellar is a threat exposure management platform that enables enterprises to detect and respond to network threats before they escalate. As a platform and API provider, NordStellar can provide insight into threat actors’ activities and their handling of compromised data. Designed by Nord Security, the company renowned for its globally acclaimed digital privacy tool NordVPN.
About Version 2 Limited
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.



