Summary: Uncover the critical differences between the deep web and dark web, understand their cybersecurity risks, and learn why proactive monitoring is essential to protect your business from modern cyber threats.
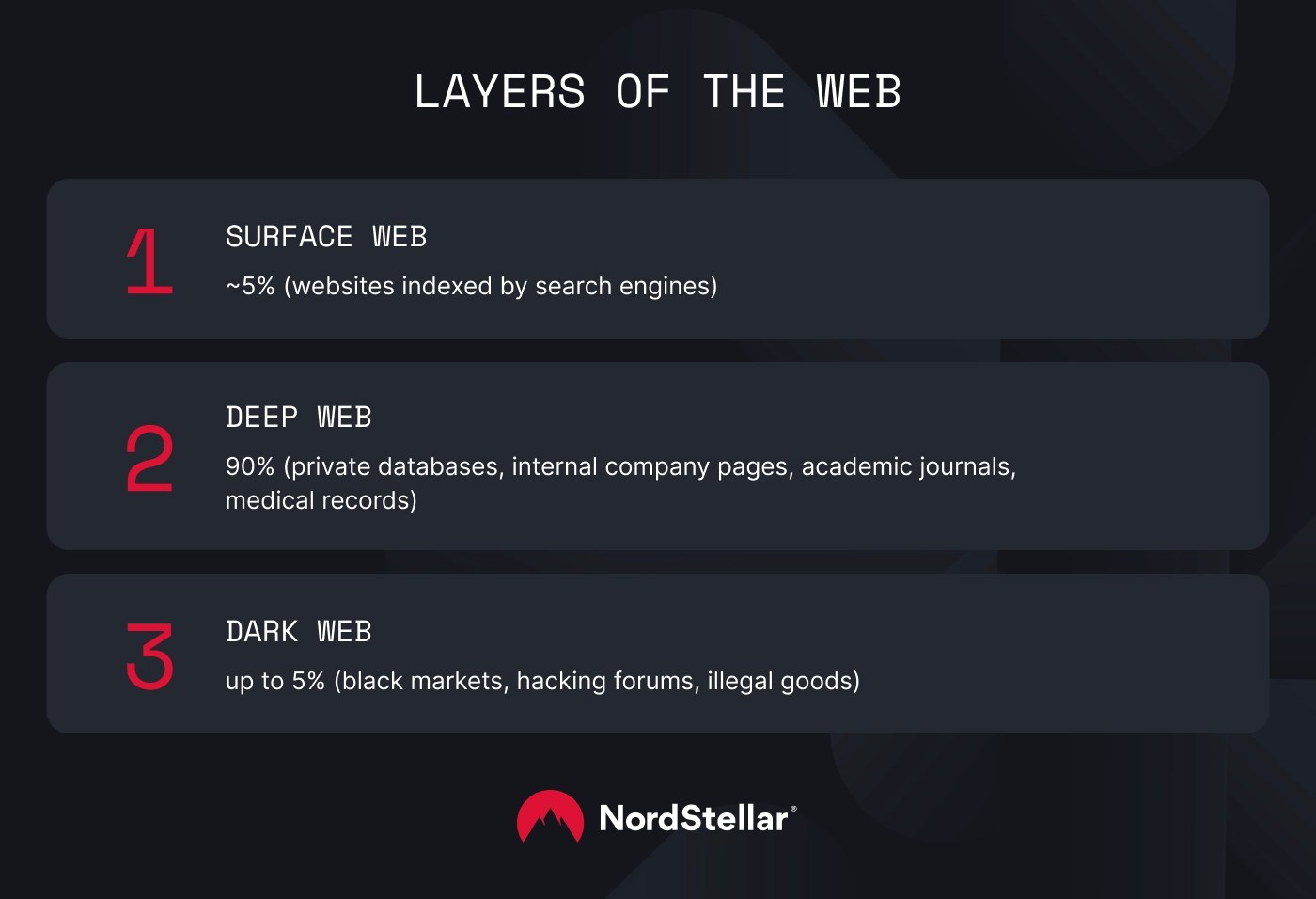
The internet is far more than the visible web. Like the mass of an iceberg, most information and web pages lie below the surface.
The hidden corners of the web can be “deep” – buried beneath the surface, but easy to uncover. However, they can also be “dark” – allowing criminal activity to flourish without surveillance.
Understanding the difference between the deep web and the dark web could be critical to your enterprise cybersecurity. This article will explain how the deep and dark web differ and provide valuable tips for securing sensitive data.
What is the deep web?
The deep web includes web content that is not indexed by search engines. This may seem trivial, but it amounts to vast amounts of data.
For instance, Google appears comprehensive. However, its web crawler index is less than five percent of the World Wide Web. The rest remains on the deep web, and you can’t reach it via traditional search engine results.
Pages on the deep web include password-protected sites like private databases, internal company pages, academic journals, and medical records. Web browsers can often access these pages with the correct credentials, but search engine crawlers cannot process them.
Most deep web content is not malicious. Universities and medical providers need to keep confidential content out of the public eye. Website owners often use the robots.txt file to manage traffic and determine what data search engines can access.
The critical takeaway when comparing deep web vs dark web content is that the deep web is publicly accessible without special browser tools. Anyone with the right credentials can gain access. That’s why criminals prefer the more private environment of the dark web.
What is the dark web?
The dark web is a section of the deep web protected by multiple layers of encryption.
Users can only access dark web servers via special browsers like Tor (the Onion Router). The Tor browser uses randomization to route traffic through virtual tunnels before granting access. This architecture anonymizes users and complicates dark web monitoring.
Ordinary browsers cannot access dark web sites due to unique registry operators. Web crawlers cannot penetrate the encryption protecting dark web servers. Without Tor or other specialist tools, access is impossible.
The dark web emerged in 2000 as a decentralized platform for anonymous communication. In theory, it remains a valuable tool – enabling secure communication for whistle-blowers and individuals in repressive states. However, it has also become a haven for illegal activities.
Dark web marketplaces allow data thieves to sell credentials and other sensitive information. Hackers plan data breaches on dark web forums, while merchants sell many types of illegal goods to customers worldwide.
What is the surface web?
Both the dark web and the deep web exist beneath the surface web. The surface web includes websites indexed by search engines like Google or Bing.
For most internet users, the surface web is all they see. However, the visible web is only a small fraction of all web traffic. 90–95% of web content is submerged and wholly or partially inaccessible via browsers like Google Chrome.
Deep web vs dark web: key differences
The table below provides a quick deep web vs dark web comparison to understand the differences between the two:
| | |
|---|
| Accessible via normal web browsers. | Only accessible via special tools (such as the Tor browser or the Invisible Internet Project) |
| Massive, containing more than 90% of the internet, consisting of hundreds to thousands of exabytes of data, eclipsing both the surface web and dark web. | Relatively small subset of the deep web, estimated at 0,01–5% of the total internet or around 150,000 websites, with only a few thousand unique sites globally. |
| Visible to web browsers, provided users have the appropriate credentials. | Invisible to ordinary web browsers due to strong encryption. |
| Relatively low. Deep web content may include confidential data, requiring robust access controls and encryption. However, most content is benign and carries a low threat level. | High. Criminal collectives routinely use dark web sites for illegal activities like planning cyber attacks, sharing leaked credentials, and selling exploit or ransomware-as-a-service kits. If credentials appear on dark web forums, companies should anticipate their use in future attacks. |
| Low. Companies often use the deep web in everyday operations. Deep web sites may host illegal content (such as torrents). However, using the deep web for legitimate reasons is uncontroversial. | Many dark web sites carry a high legal risk due to illegal activities. Using Tor to browse the dark web is legal, although participation is not advisable. |
Why the difference matters for businesses
The differences above matter for one core reason: the dark web functions as a clearinghouse for illegal activities. Cyber threats hatched on the dark web steal data, disrupt business operations, and lead to severe regulatory and reputational damage.
Attackers may collaborate on dark web forums to share information and create sophisticated phishing campaigns, use off-the-shelf exploit kits to leverage backdoors, or mobilize stolen login credentials in brute-force attacks.
This situation challenges risk analysts and security teams to discover leaked credentials and gather threat intelligence. Companies need to update their threat prevention techniques to monitor dark web environments.
Dark web threats also pose a critical compliance challenge. Regulators penalize businesses that put customer data at risk. Data protection increasingly requires active dark web monitoring to manage compliance risks.
These factors make integrating dark web security into your risk management strategy critical. Security teams need to upgrade their capabilities. Analysts need security tools to track dark web activities, while engineers must implement alerting systems and controls to counter threats before they escalate.
How to monitor dark web activity for business security
The next cybersecurity threat to your critical systems and data could be incubating on the dark web as you read this. Without visibility and dark web intelligence, security teams can only wait and hope their network defenses are sufficiently robust.
Fortunately, monitoring solutions work around this problem, giving security analysts advanced warning of dark web discussions and potential threats.
Dark web monitoring tools search for your information. They detect stolen employee logins, customer data, postal addresses, social security numbers, and other valuable personal data relating to your business operations.
Monitoring tools can also scan for intellectual property and other confidential information, helping you manage the threat posed by malicious insiders and corporate espionage.
Moreover, dark web monitoring happens in real time. Monitoring tools detect compromised data and automatically generate alerts. Security teams gain time to mitigate potential threats (for example, by requesting password changes for affected users).
NordStellar’s threat intelligence platform is a great example. Data breach monitoring continuously tracks marketplaces and forums, informing security teams when sensitive data appears on the dark web. Meanwhile, account takeover prevention monitors privileged employee and customer accounts for stolen credentials or suspicious activity. Active scanning identifies hijacks at an early stage before damage results.
Security analysts can also use monitoring tools for threat-hunting expeditions. Cyber threat intelligence helps analysts learn about active groups and attack techniques – generating research outcomes to improve the company’s security posture.
Legal and ethical considerations of accessing dark web content
Companies should actively monitor the dark web for security threats. However, it’s important to stress that not all security actions on the dark web are legally safe or advisable from an ethical perspective.
Firstly, we should clarify what is legally permitted when investigating dark web threats. Using Tor and accessing dark web servers is legal. Companies can passively monitor activity and data sales on dark web marketplaces.
There’s nothing wrong with simply accessing dark web sites. Most countries allow free access, although the Tor browser is illegal in China, Russia, and Iran.
However, engaging with threat actors on the dark web creates risks wherever you are. Exposed investigators could receive inaccurate information or provoke cyberattacks. If discovered, automated scanning tools could mark companies as targets for reprisals by criminal groups.
Investigators could also accidentally encounter illegal content while browsing marketplaces and forums. This creates a legal risk (possession of harmful images or confidential data). Monitoring dark web forums also poses ethical questions.
For instance, should you continue to monitor forums despite knowing they host illegal transactions? Or should you inform law enforcement agencies and trust them to intervene?
These operational, legal, and ethical issues make clear policies about accessing the dark web are critically important. Security teams (and anyone else tasked with dark web access) should know how to do so safely – and how to report legal queries if they arise.
We would also advise consulting your legal team when writing dark web security policies. Legal advice ensures you stay on the right side of the law while benefiting from dark web threat monitoring.
Incident examples: When corporate data hits the dark web
The dark web is more than a distant threat hidden deep within the internet. As a couple of real-world examples show, it’s an active site for the preparation and monetization of cyber attacks.
AT&T’s unexpected dark web data breach
In March 2024, communications giant AT&T discovered that 76 million customer records were being sold via dark web marketplaces. The data included SSNs, home addresses, and login credentials of current and past clients.
Although a vast database was available for sale, the company stated that it had found no evidence of data breaches. This highlights the need for proactive monitoring that anticipates breaches, not waiting for the symptoms of cyber attacks.
LinkedIn: An entire social media ecosystem exposed on the dark web
Social media platforms have also suffered dark web data breaches. In 2021, LinkedIn disclosed the exposure of 700 million user records. The data included phone numbers, email addresses, and other personally identifiable information – a gold mine for phishers.
In this case, attackers leveraged code flaws in the platform’s API, allowing them to scrape confidential information about users and their connections.
Although the company has not disclosed details of the impact, the incident likely dented LinkedIn’s reputation as a trusted platform for networking and professional communication. It may also have influenced a gradual decline in ad revenue, harming the platform’s finances.
Colonial Pipeline: Using the dark web as a market for RaaS products
The 2021 Colonial Pipeline ransomware attack shut down a critical energy pipeline on the Eastern Seaboard, leading to a $4.4 million ransom payment. Attackers used stolen employee credentials to access an unused Virtual Private Network account that remained accessible and active.
The critical facts are that attackers used stolen credentials purchased on the dark web. Attackers also used a ransomware-as-a-service (RaaS) kit supplied by the DarkSide collective via dark web marketplaces.
Proactive threat intelligence gathering may have enabled Colonial Pipeline to detect attack planning and locate stolen credentials. However, the company relied on legacy security systems and did not account for dark web threats.
Final thoughts on managing deep and dark web exposure
The surface web is deceptive. Underneath lies a bottomless ocean of deep web content. And within that ocean, the protected dark web provides a secure refuge for illegal activities.
As we’ve learned, these illegal activities could target your company. Data from your employees or customers could be changing hands on dark web marketplaces while criminals build phishing profiles or plan data theft attacks.
Managing deep and dark web exposure is now a fundamental online safety requirement. Security teams should assume their data is available via onion sites and use monitoring platforms like NordStellar to verify the degree of exposure.
Dark web monitoring complements access controls, network segmentation, and intrusion detection and response tools. Dark web intelligence and endpoint protection protect against hidden threats, while employee training helps manage phishing risks.
Ready to strengthen your defenses against hidden online threats? Don’t wait for a breach to act – contact the NordStellar team today and proactively update your data security strategy.






 Research: Ransomware Attacks Spiked by 49% in the First Half of 2025
Research: Ransomware Attacks Spiked by 49% in the First Half of 2025