The biggest data breaches in history have set new records. According to the Identity Theft Resource Center data, in the first half of 2024, over 1 billion US consumers had their personal information exposed — a 490% increase from 2023[1]. The consequences are severe — businesses are losing millions in lawsuits and facing reputational damage, individuals are dealing with identity theft and fraud, and governments are enforcing stricter regulations and demanding stronger data security measures.
While the risks posed by data breaches continue to grow, companies can take action and protect themselves. In this article, we examine the biggest data breach examples from 2020 to 2024, key trends shaping cybersecurity, and steps companies can take to protect their data.
1. National Public Data (NPD) breach
Date the data breach occurred: April 2024
Cause: Hacking
Countries affected: The United States, Canada, and the United Kingdom
Number of records exposed: 2.9 billion
People affected: Up to 170 million
Types of data compromised: Social Security numbers (SSNs), names, dates of birth (DOBs), email addresses, phone numbers, and mailing addresses
Discovery and announcement
In August 2024, security researchers found around 2.9 billion stolen National Public Data records for sale on dark web forums. The discovery raised alarms and led to an internal investigation. Shortly after, the company confirmed the breach.
Response
In response to the huge data breach, National Public Data collaborated with law enforcement and conducted a thorough review of affected records to assess the impact. The company strengthened its data security measures to prevent future incidents.
National Public Data also provided instructions on obtaining free credit reports from Equifax, Experian, and TransUnion. Additionally, it recommended users place fraud alerts or consider a credit freeze to mitigate the risks of identity theft.
Impact
The NPD data breach not only exposed billions of records but also led to the collapse of the company. After intense scrutiny, regulatory investigations, and mounting legal challenges, NPD declared bankruptcy in October 2024 and ceased operations[2], [3].
2. Mother of all breaches (MOAB)
Date the breach was discovered: January 2024
Cause: Compilation of multiple data breaches
Countries affected: Multiple
Number of records exposed: 26 billion
People affected: Hundreds of millions
Types of data compromised: Usernames, passwords, email addresses, and other sensitive information
Discovery and announcement
In January 2024, security researcher Bob Diachenko and Cybernews investigators uncovered a huge data breach known as the “Mother of all breaches” (MOAB). The dataset contained approximately 26 billion records compiled from 3,876 websites, combining data from numerous past cybersecurity breaches.
Major platforms like LinkedIn, Twitter, Adobe, and Dropbox were among the affected sources. The breach also included records from government organizations in the US, Brazil, Germany, the Philippines, Turkey, and several other countries. Leak-Lookup, a data breach search engine, admitted it was the holder of the leaked dataset.
Response
Leak-Lookup attributed the breach to a “firewall misconfiguration” that has since been fixed. In response, Cybernews updated its data leak checker to include MOAB-related information, which would allow users to check if their data was exposed in one of the biggest data breaches to date.
Impact
The MOAB breach exposed the dangers of large-scale data collection and the lasting damage caused by repeated data security failures. By combining stolen records from thousands of past incidents, this breach significantly increased the risk of identity theft, fraud, and cyberattacks. With so much sensitive personal data in one place, hackers can easily locate and exploit exposed credentials, launch targeted phishing scams, and take over accounts.
The breach also raised concerns about how long companies store sensitive user data. It underscored the need for stricter policies to limit data retention and improve security. Even old breaches, once considered isolated incidents, can resurface in massive leaks like this, putting millions at risk. As of January 2024, MOAB is almost certainly the largest data breach ever discovered[4].
3. Financial Business and Consumer Solutions (FBCS) data breach
Date discovered: February 26, 2024
Cause: Unauthorized access to FBCS’s internal network
Countries affected: Primarily the United States
Number of records exposed: Undisclosed
Number of people affected: Undisclosed
Types of data compromised: Names, addresses, DOBs, SSNs, driver’s license and state identification numbers, medical claims, provider and clinical information, and health insurance details
Discovery and announcement
On February 26, 2024, FBCS detected unauthorized access to certain systems within its network. Investigators found that hackers had access to FBCS systems from February 14 to February 26, 2024.
During this time, they could view or acquire sensitive information stored on the network. To assess the impact, FBCS conducted a full review to determine what data was at risk and who was affected.
Response
After discovering the breach, FBCS took immediate action to investigate and contain the incident. The company reported the matter to federal law enforcement and worked with forensic specialists to understand how the breach occurred and prevent future attacks.
To strengthen security, FBCS built a new, more secure environment with additional safeguards to protect sensitive data. The company also urged affected individuals to remain vigilant against potential identity theft and fraud.
Impact
One of the biggest data breaches in 2024 exposed highly sensitive personal and healthcare information, which put individuals at risk of identity theft and medical fraud. Stolen SSNs and medical records could be misused for fraudulent insurance claims, unauthorized medical treatments, or financial scams[5].
4. Ticketmaster data breach
Date discovered: May 2024
Cause: Unauthorized access to a cloud database hosted by a third-party data services provider
Countries affected: The United States, Canada, and Mexico
Number of records exposed: Undisclosed
People affected: Customers who purchased tickets to events in North America
Types of data compromised: Email addresses, phone numbers, encrypted credit card information, and other personal details provided during ticket purchases
Discovery and announcement
In May 2024, Ticketmaster detected unauthorized activity in an isolated cloud database managed by a third-party provider. The company launched a full investigation with cybersecurity experts and notified the relevant authorities. The investigation confirmed that no further unauthorized access occurred beyond the initial incident.
Response
Ticketmaster worked with law enforcement, banks, and credit card companies to investigate the breach and mitigate its impact. Affected customers were offered a free 12-month identity monitoring service from a leading provider. Customers were also advised to monitor their bank and credit card statements for suspicious transactions and report any unauthorized activity immediately.
Impact
The Ticketmaster breach raised concerns about the security of third-party data storage and the risks customers face when trusting companies with personal and payment information. Although the company encrypted payment card data, hackers could still use exposed contact details for phishing scams, fraud attempts, and identity theft[6].
5. Change Healthcare data breach
Date discovered: February 21, 2024
Cause: A cybercriminal gained unauthorized access to Change Healthcare’s computer system and deployed ransomware
Countries affected: Primarily the United States
Number of records exposed: Undisclosed
People affected: Patients, healthcare providers, and insurers relying on Change Healthcare’s services
Types of data compromised: Names, contact details, DOBs, health insurance information, SSNs, government-issued IDs, medical records, diagnoses, medications, test results, financial data, and payment details
Discovery and announcement
On February 21, 2024, Change Healthcare detected ransomware activity in its systems. The company immediately shut down affected systems, disconnected its network to contain the attack, and launched an investigation with law enforcement and leading cybersecurity experts.
Response
On July 29, 2024, Change Healthcare began notifying affected individuals by mail. To contain the breach, the company shut down systems and severed network connections to stop further access. It also strengthened security policies and implemented additional safeguards to prevent future incidents.
Change Healthcare worked with cybersecurity experts to monitor both the clear and dark web for any misuse of stolen data. The company offered affected individuals free credit monitoring and identity protection services through IDX for two years, covering all costs.
Impact
One of the biggest data breaches in the healthcare industry had serious consequences for patients, healthcare providers, and insurers. Stolen medical records and insurance details could be used for identity theft, fraudulent claims, or financial fraud[7], [8].
6. AT&T data breach
Date discovered: April 19, 2024
Cause: Unauthorized access to AT&T’s workspace on a third-party cloud platform
Countries affected: Primarily the United States
Number of records exposed: Undisclosed
People affected: Both current and former AT&T customers, as well as customers of mobile virtual network operators (MVNOs) using AT&T’s wireless network
Types of data compromised: Records of customer call and text interactions, including telephone numbers and, for some records, associated cell site identification numbers
Discovery and announcement
On April 19, 2024, AT&T learned that a threat actor had unlawfully accessed and copied its call logs. The company immediately launched its incident response plan and brought in external cybersecurity experts to investigate.
The breach took place between April 14 and April 25, 2024. During this period, hackers stole files containing customer call and text records from May 1 to October 31, 2022, and January 2, 2023.
Response
AT&T quickly closed the unauthorized access point and worked with law enforcement to arrest those involved in the incident. The company notified both current and former customers whose information was compromised and provided resources to help protect their data.
Impact
The breach exposed call and text records from nearly all of AT&T’s wireless customers, including those using AT&T’s network through MVNOs and landline customers who interacted with these numbers during the specified periods.
Although the compromised data didn’t include content from communications or other sensitive personal information, the exposure of phone numbers and associated cell site identification numbers raised significant privacy concerns[9], [10].
7. Dell customer information data breach
Date the breached data was posted on the dark web: April 28, 2024
Cause: Unauthorized access to a Dell portal
Countries affected: The United States, China, India, Australia, and Canada
Number of records exposed: 49 million customer records
People affected: Dell customers who made purchases between 2017 and 2024
Types of data compromised: Customer names, physical addresses, Dell hardware details, order and warranty information
Discovery and announcement
On May 9, 2024, Dell confirmed unauthorized access to a database containing customer information related to sales. Dell clarified that no financial or other personal data, such as email addresses, phone numbers, or passwords, were exposed.
Response
Dell took immediate action to contain the breach, activated its incident response procedures, and involved external cybersecurity experts to investigate the scope of the attack. The company notified law enforcement and worked to secure its systems further. It also informed the customers of the breach and gave advice on how to safeguard their information.
Impact
The breach exposed the personal information of approximately 49 million customers, particularly affecting those who made purchases from Dell between 2017 and 2024[11], [12].
8. Synnovis data breach
Date of attack: June 3, 2024
Cause: Ransomware cyberattack
Country affected: The United Kingdom
Data exposed: Approximately 400 GB of data
People affected: Patients and healthcare providers in South East London
Types of data compromised: Names, NHS numbers, and test codes
Discovery and announcement
On June 3, 2024, Synnovis, a partnership providing pathology services to several NHS organizations in South East London, experienced a ransomware attack that disrupted all IT systems and affected sample processing and result transmission.
On June 20, a cybercriminal group claiming responsibility for the attack published data online and claimed it was stolen from Synnovis. Synnovis confirmed that the data was from its administrative systems.
Response
In response to the breach, Synnovis worked closely with law enforcement, the Information Commissioner, the National Cyber Security Centre, and NHS England. It began a comprehensive investigation and took immediate steps to contain the breach and restore operations.
Synnovis publicly apologized for the disruptions caused to patients and healthcare services and reaffirmed its commitment to preventing future incidents. The company urged affected patients to attend scheduled appointments unless instructed otherwise and continued to provide updates to the public regarding the impact on services.
Impact
The ransomware attack caused major disruptions, including delays in test result processing and appointment cancellations. While emergency care remained operational, the breach affected many non-urgent services in South East London. It took the company until late autumn to restore access to all services that were available before the cyber attack.
Although the breach didn’t expose any sensitive clinical data, it severely impacted essential healthcare services, resulting in significant financial losses. According to company accounts, the estimated cost of the breach was £32.7 million — well above Synnovis’ 2023 profits of £4.3 million[13], [14], [15], [16], [17].
9. The 2023 Twitter (now X) data breach
Date discovered: January 4, 2023
Cause: A vulnerability in Twitter’s application programming interface (API) that allowed unauthorized access to user data
Countries affected: Multiple
People affected: Over 200 million Twitter users
Types of data compromised: Email addresses and phone numbers
Discovery and announcement
In January 2023, a hacker forum published a database containing the email addresses and usernames of over 200 million Twitter (now X) users. The data was sold for eight credits of the forum’s currency, worth approximately $2.
It was released as a RAR archive, which consisted of six text files totaling 59 GB of data. It was reportedly collected by exploiting a vulnerability in Twitter’s API between June 2021 and January 2022. BleepingComputer confirmed the validity of many of the email addresses listed in the leak.
Response
Twitter stated that it found no evidence the data was obtained through a vulnerability in its systems. The company suggested that the data might have been collected from publicly available sources.
Impact
The breach made it easier to link Twitter handles to real identities, potentially exposing these individuals to harm, retaliation, or surveillance. Verified users, including celebrities and politicians, were particularly vulnerable to extortion or manipulation because hackers could potentially exploit their data for malicious purposes[18], [19].
10. Progress Software data breach (MOVEit vulnerability)
Date discovered: May 2023
Cause: Zero-day vulnerability in Progress Software’s MOVEit Transfer application
Countries affected: Primarily the United States
People affected: Over 94 million users
Types of data compromised: Names, SSNs, banking details, and other confidential records
Discovery and announcement
On May 31, 2023, Progress Software identified a critical zero-day vulnerability (CVE-2023-34362) in its MOVEit Transfer application, a managed file transfer solution widely used across various sectors. This vulnerability, which stemmed from an SQL injection flaw, allowed unauthorized access to sensitive data within MOVEit Transfer’s databases.
Response
Progress Software acted swiftly upon discovering the vulnerability. Within 48 hours, the company initiated an investigation, alerted MOVEit customers, and provided immediate mitigation steps.
On June 15, 2023, Progress released a security patch to address the flaw. The company temporarily took MOVEit Cloud offline to prevent further exploitation while applying patches.
Impact
The MOVEit breach significantly affected thousands of organizations globally. Progress Software reported $951,000 in cyber incident and vulnerability response expenses during its fiscal third quarter, which ended August 31, 2023.
Additionally, Progress Software faced 58 class-action lawsuits and received a subpoena from the US Securities and Exchange Commission (SEC). However, in August 2024, the SEC concluded its investigation and decided not to recommend any enforcement action against the company.
Despite this, as of this article’s publication, Progress Software continues to face hundreds of class-action lawsuits centralized in Massachusetts federal courts[20], [21], [22], [23], [24].
11. T-Mobile data breach
Date discovered: January 5, 2023
Cause: Unauthorized access via an exposed application programming interface (API)
Country affected: The United States
Number of records exposed: 37 million customer accounts
People affected: Current postpaid and prepaid customers of T-Mobile in the US
Types of data compromised: Customer names, billing addresses, email addresses, phone numbers, DOBs, T-Mobile account numbers, number of lines on the account, and service plan features
Discovery and announcement
On January 5, 2023, T-Mobile confirmed a data breach after a thorough investigation. The investigation found that a bad actor exploited an exposed application programming interface (API) to access limited customer information.
Response
Within 24 hours of detection, T-Mobile shut down the compromised API to prevent further access. The company immediately implemented its incident response protocols, notified affected customers, and reassured them that their financial data remained secure. It emphasized that no customer accounts were at direct risk.
Impact
While T-Mobile didn’t expect a significant impact on its business operations, it acknowledged the potential effect on customer trust. To address this, the company pledged to invest in cybersecurity improvements to better protect its customers and prevent future breaches.
In addition, on September 30, 2023, T-Mobile reached a $31.5 million settlement to resolve a probe by the Federal Communications Commission (FCC) into major data breaches that occurred over a three-year period. As part of the settlement, T-Mobile was required to pay a $15.75 million civil penalty and spend another $15.75 million over the next two years to strengthen its cybersecurity program[25], [26].
12. HCA Healthcare data breach
Date discovered: July 5, 2023
Cause: Theft from an external storage location
Country affected: The United States
Number of records exposed: 27 million rows of data
People affected: 11 million HCA Healthcare patients
Types of data compromised: Patient names, cities, states, ZIP codes, email addresses, phone numbers, DOBs, genders, service dates, facility locations, and upcoming appointment details
Discovery and announcement
On July 5, 2023, HCA Healthcare discovered that an unauthorized party had posted a list containing patient information on an online forum. The stolen data came from an external storage location used for formatting email communications, like appointment reminders and healthcare education messages.
On July 10, 2023, the company announced the breach in a press release, outlined its response plan, and began assessing the full impact.
Response
Upon discovering the breach, HCA Healthcare promptly disabled access to the compromised storage location and enrolled third-party experts for a comprehensive investigation. The company also reported the incident to law enforcement.
On July 14, 2023, HCA Healthcare began notifying impacted patients via email and mailed official notification letters. Shortly after, the company launched a dedicated webpage for real-time updates. To support affected individuals, it offered credit monitoring and identity protection services.
Impact
The breach didn’t disrupt patient care or operations but raised concerns about potential phishing attacks that may target affected individuals. HCA Healthcare advised patients to remain cautious of unsolicited communications asking for sensitive personal information. The company reported no financial costs[27], [28].
13. Cash App data breach
Date discovered: April 2022
Cause: Unauthorized access by a former employee
Country affected: The United States
People affected: 8.2 million users
Types of data compromised: Names, brokerage account numbers, portfolio values, holdings, and stock trading activity for one day
Discovery and announcement
In December 2021, a former employee of Block, Inc., the parent company of Cash App, accessed and downloaded sensitive customer data without authorization. Four months later, the company discovered the breach.
The discovery prompted Block to file a report with the US Securities and Exchange Commission (SEC). The compromised data was related to users of Cash App Investing, which is separate from Cash App’s primary peer-to-peer payment service.
Response
Once the breach was identified, Block acted quickly to launch an internal investigation and notify law enforcement. The company also brought in a leading forensics firm to help assess the scope of the breach.
Block notified approximately 8.2 million affected current and former customers. The company also provided them with clear information about the breach and offered guidance on how to protect their accounts.
Impact
Although hackers did not access critical personal details, the breach raised concerns about internal security practices and data protection measures. In response, Block agreed to a $15 million settlement to address allegations of negligence and compensate affected customers[29], [30].
14. The 2022 Twitter (now X) data breach
Date discovered: July 21, 2022
Cause: API vulnerability
Countries affected: Multiple
Number of records exposed: Details of 5.4 million Twitter accounts
People affected: 5.4M users
Types of data compromised: Usernames, phone numbers, and email addresses
Discovery and announcement
In January 2022, Twitter (now known as X) was alerted to a vulnerability through its bug bounty program. This flaw allowed anyone to submit an email address or phone number to Twitter’s systems and identify the associated account.
The issue stemmed from a code update in June 2021. Twitter immediately fixed the flaw, and no exploitation was detected at that time. However, in July 2022, a report revealed that someone had exploited the vulnerability and was selling the collected data. Twitter confirmed the breach after reviewing the available data.
Response
Twitter acted quickly by notifying affected account owners. To protect users operating pseudonymous accounts, the company advised all users not to link publicly known phone numbers or email addresses to their accounts. Twitter also recommended enabling two-factor authentication for added security.
Impact
The breach exposed contact details — phone numbers and email addresses — for 5.4 million Twitter accounts. While much of the data was publicly available, hackers could still potentially use it in targeted phishing attacks and compromise users who wanted to remain anonymous[31], [32].
15. Syniverse data breach
Date discovered: May 2021
Cause: Unauthorized access to Syniverse’s electronic data transfer (EDT) environment
Countries affected: Multiple
Number of records exposed: Unknown
People affected: Customers of 235 telecom carriers, potentially billions of individuals whose messages and call records were processed by Syniverse
Types of data compromised: Login credentials for carrier customers, call records, data usage details, and text message routing information
Discovery and announcement
In May 2021, Syniverse discovered that an unknown individual or group had gained unauthorized access to its electronic data transfer (EDT) environment. The breach had been ongoing since May 2016, which means that attackers had access to sensitive information for nearly five years before the company discovered the breach.
On September 27, 2021, Syniverse disclosed the breach in a filing with the US Securities and Exchange Commission (SEC). The company confirmed that the breach impacted 235 telecom customers, but the potential number of affected individuals could be in the millions or even billions.
Response
Upon discovery, Syniverse activated security protocols and hired a top-tier forensics firm to investigate. The company reset or deactivated all affected customer credentials to prevent further access.
Syniverse notified law enforcement agencies, cooperated with investigators, and implemented stronger security measures to prevent future breaches. However, the company didn’t notify individual users directly. Instead, it relied on telecom customers to inform impacted subscribers.
Impact
The breach raised concerns because Syniverse handles inter-carrier messaging and data routing for major telecom operators. While the full extent is still unclear, cybersecurity experts speculated that the breach could have been a state-sponsored attack because no ransom demands or attempts to sell the data were observed[33], [34].
16. Facebook (Meta) data breach
Date discovered: April 2021
Cause: Scraping due to a vulnerability in Facebook’s feature
Number of countries affected: 106 countries
Number of records exposed: Unknown
People affected: 533 million Facebook users
Types of data compromised: Phone numbers, Facebook IDs, names, locations, DOBs, bios, and email addresses
Discovery and announcement
In April 2021, personal data from over 533 million Facebook users across 106 countries was leaked online. Hackers obtained the data through a vulnerability in Facebook’s “Contact importer” feature, which Facebook claimed to have patched in 2019.
Response
A Facebook spokesperson stated that the data was scraped due to the vulnerability in the “Contact importer” feature. However, Facebook didn’t notify affected users and argued that the data was publicly available.
Further investigation showed that Facebook planned to downplay the leak as an industry-wide issue rather than an isolated security failure. An internal email from April 2021 revealed the company’s strategy to minimize press coverage of the breach.
Impact
The exposed data posed risks, including potential impersonation, scams, and social engineering attacks. In November 2022, the Irish Data Protection Commission fined Meta Platforms, Facebook’s parent company, $276 million for violating GDPR regulations. This fine contributed to Meta’s reputation for receiving some of the largest data breach fines under GDPR[35], [36], [37], [38].
17. Microsoft data breach
Date discovered: January 2021
Cause: Exploitation of four zero-day vulnerabilities
Countries affected: Primarily the United States and several countries in Europe
Number of records exposed: Not explicitly quantified
Servers affected: Approximately 250,000 servers worldwide
People affected: Undisclosed
Types of data compromised: Emails, email attachments, user credentials, and administrative privileges on affected servers
Discovery and announcement
In early January 2021, cybersecurity firm Volexity discovered unusual activity on Microsoft Exchange Servers, which led to the identification of a major breach. Attackers exploited four zero-day vulnerabilities in the Exchange Server, collectively known as “ProxyLogon,” which allowed them to access email accounts, passwords, and administrative privileges.
The attackers used this access to move laterally within networks and installed web shells — malicious scripts that provided ongoing access, even after the vulnerabilities were patched. On March 2, 2021, Microsoft publicly disclosed the vulnerabilities.
Response
Upon discovering the breach, Microsoft acted swiftly and released security patches for Exchange Server versions 2010, 2013, 2016, and 2019. The company urged organizations to implement these patches immediately to close the vulnerabilities.
However, simply applying the patches didn’t remove the web shells already installed by the attackers. Organizations were advised to conduct thorough investigations to identify and remove any remaining threats and ensure their systems were secure.
Impact
The breach affected about 250,000 servers worldwide. In the United States alone, it compromised approximately 30,000 organizations. The breach impacted various sectors, including healthcare, legal, higher education, defense, policy think tanks, and small businesses.
The exposed stolen data could potentially lead to intellectual property theft, espionage, and further malicious activities, such as ransomware deployment on some compromised servers. The scale and severity of the attack make it one of the largest and most damaging cyber incidents in recent US history[50], [51], [52].
18. SolarWinds data breach
Date discovered: December 2020
Cause: Supply chain attack
Countries affected: Primarily the United States, but also the United Kingdom, Canada, Mexico, Spain, Israel, the United Arab Emirates, and other countries
Number of records exposed: Undisclosed, but numerous US federal agencies and private sector companies were affected
People affected: More than 18,000 SolarWinds customers
Types of data compromised: Emails, confidential documents, internal communications, and potentially sensitive government and corporate data
Discovery and announcement
In December 2020, cybersecurity firm FireEye discovered a cyberattack targeting SolarWinds’ Orion software, a widely used IT management platform. Investigations revealed that the attackers had infiltrated SolarWinds as early as September 2019 and were testing their ability to inject malicious code.
By February 2020, they successfully inserted trojanized code into Orion’s software updates, which SolarWinds unknowingly distributed. This backdoor, named SUNBURST, granted remote access to infected systems.
Response
On December 13, 2020, the Cybersecurity and Infrastructure Security Agency (CISA) issued an emergency directive for federal agencies to disconnect SolarWinds Orion products. The White House’s National Security Council formed a Cyber Unified Coordination Group to lead the response.
SolarWinds worked with law enforcement and cybersecurity experts to investigate the breach and released patches to fix the vulnerability. Microsoft and other security firms helped reroute malicious traffic to limit further exploitation. Congress held hearings to assess the risks to the IT supply chain and urged stricter regulations for government contractors handling extremely sensitive data.
Impact
The SolarWinds breach is one of the most significant cybersecurity incidents in history, which affected multiple US federal agencies, including the Departments of Treasury, Commerce, State, Homeland Security, and the National Nuclear Security Administration.
The breach exposed vulnerabilities in supply chain security and raised concerns about espionage and cyber warfare. While not all 18,000 customers were exploited, high-value targets, such as US government agencies and Fortune 500 companies, were specifically targeted.
In response to the breach, the US government formally blamed Russia’s Foreign Intelligence Service (SVR) for orchestrating the attack. The US administration identified the breach as part of a broader campaign of cyber espionage linked to the Russian government.
In April 2021, the Biden administration imposed sanctions on Russia. Additionally, the US Securities and Exchange Commission (SEC) fined several tech firms for failing to disclose cybersecurity risks related to the breach[39], [40], [41], [42].
19. MGM Hotels data breach
Date discovered: July 2019
Cause: Unauthorized access to an exposed cloud database
Countries affected: Primarily the United States
Number of records exposed: Tens of millions of private customer data records
People affected: More than 10.6 million hotel guests
Types of data compromised: Names, home addresses, phone numbers, emails, DOBs
Discovery and announcement
In July 2019, MGM Resorts suffered a large data breach when an unauthorized party accessed a cloud database containing information of millions of guests, including regular travelers, celebrities, tech executives, journalists, and government officials. Although MGM stated that the compromised data was “old,” many contact details were still valid.
Response
After discovering the breach, MGM hired two cybersecurity firms to investigate. While the company notified affected customers of the breach, it didn’t make a public disclosure until cybercriminals exposed the breached data in 2020. Experts criticized the delayed public disclosure and MGM’s lack of transparency.
Impact
The exposed data presented significant security risks, especially for high-profile guests. While MGM stated the breach didn’t affect operations, the leak damaged the company’s reputation and highlighted vulnerabilities in its data protection practices. The breach led to class-action lawsuits and a $45 million settlement, which also covered damages from later cybersecurity incidents.
In September 2023, MGM experienced another major data breach, which further heightened concerns about its data security practices[43], [44].
20. Marriott International data breach
Date discovered: End of February 2020
Cause: Unauthorized access using compromised employee login credentials
Countries affected: Multiple
People affected: 5.2 million guests
Types of data compromised: Contact details (name, address, email, phone), loyalty account info (account number, points balance), personal details (company, gender, birthday), preferences (room type, language), linked partnerships (airline loyalty programs)
Discovery and announcement
In late February 2020, Marriott discovered that an unexpected amount of guest information had been accessed using the login credentials of two employees at a franchise property. The unauthorized activity likely began in mid-January 2020.
Response
Upon discovery, Marriott disabled the compromised credentials and initiated an investigation. The company increased monitoring and provided resources to inform and assist guests. It also notified relevant authorities and cooperated with their investigations.
On March 31, 2020, Marriott emailed affected guests, set up a dedicated website, and provided call center resources. Marriott also offered free enrollment in the IdentityWorks personal information monitoring service for one year, provided by Experian.
Impact
The breach exposed the sensitive information of 5.2 million guests. While the breach didn’t compromise financial data or encrypted passwords, it raised concerns about Marriott’s data security practices, especially in light of the 2018 breach that affected 500 million guests.
In October 2024, Marriott agreed to pay a $52 million settlement to 49 states and the District of Columbia over multiple data security failures from 2014 to 2020 that affected over 334 million customers.
As part of the settlement, Marriott and Starwood committed to improving data security. They also allowed US customers to request the deletion of their personal information and reviewed loyalty accounts for potentially stolen points[45], [46], [47].
21. CAM4 data breach
Date discovered: March 2020
Cause: A firewall failure
Countries and people affected: Primarily users from the US, Brazil, and Italy
Number of records exposed: 10 billion records
Types of data compromised: Names, email addresses, hashed passwords, country of origin, device information, gender preference, sexual orientation, payment logs (credit card type, amount paid), chat transcripts, fraud detection logs, and IP addresses
Discovery and announcement
In March 2020, cybersecurity researchers from Safety Detectives discovered that CAM4, an adult live-streaming platform, had left its Elasticsearch production database exposed online without a password. This misconfiguration allowed anyone with the correct IP address to access sensitive user information.
Response
Granity Entertainment, CAM4’s parent company, quickly secured the exposed database by removing it from public access and moving it to a secure internal network. It also deleted any personally identifiable information from the database. However, because the logs dated back to March 16, 2020, it’s possible that cybercriminals had accessed the data before the company secured it.
On May 4, 2020, Granity publicly stated that researchers and internal security teams had accessed only 93 individuals’ data. It denied that external hackers had exploited the database. Still, experts criticized CAM4 for not having sufficient security measures in place.
Impact
Although investigators found no confirmed evidence of widespread data misuse, the breach exposed users to potential blackmail, phishing, and identity theft. Users who did not use anonymous credentials risked having their real identities linked to their online activity.
While the breach didn’t receive widespread media attention, privacy experts warned that if cybercriminals had exploited the data, Granity Entertainment could have faced significant lawsuits and regulatory penalties, especially under Europe’s GDPR and other global data protection laws[48], [49].
22. Sina Weibo data breach
Date discovered: March 2020
Cause: Exploitation of a feature allowing users to find friends by uploading their phone contacts
Countries affected: Primarily China
Number of people affected: 538 million users
Types of data compromised: Names, usernames, gender, location, and phone numbers
Discovery and announcement
In March 2020, Sina Weibo, China’s leading microblogging platform, confirmed a massive data breach that affected approximately 538 million users. The breach was revealed when a hacker offered the stolen user data for sale on the dark web for $250. Weibo clarified that passwords were not exposed in the breach.
Response
After the breach, China’s Ministry of Industry and Information Technology (MIIT) summoned Weibo representatives to address the incident. The MIIT instructed Weibo to improve data security and internal management and notify users and authorities of future incidents.
Although the data breach didn’t expose any passwords, Weibo advised users who reused passwords across different platforms to take extra precautions. The company committed to strengthening its security measures and reported the breach to law enforcement.
Impact
The breach compromised the personal information of 538 million users, making it one of the world’s biggest data breaches. The stolen data increased the risk of phishing attacks, identity theft, and other malicious activities[53].
Trends and patterns in recent large data breaches
Recent major data breaches reveal several key trends and patterns:
Attackers continue to rely on common but highly effective methods, including phishing, ransomware, and supply chain attacks. Top
ransomware groups use these tactics to target organizations and maximize their impact.
Corporate data breaches expose large volumes of sensitive customer information, while government hacks raise serious national security concerns.
Industries dealing with valuable personal or financial data, including healthcare, finance, and technology, remain prime targets.
The full scale of data breaches often takes months or years to emerge.
What’s more, stolen data frequently appears on the dark web long after the initial attack, making it challenging for authorities to trace the source or hold attackers accountable. This delay puts organizations and individuals at risk without their knowledge, giving cybercriminals a significant advantage.
In response, regulatory bodies are tightening compliance requirements. Laws like GDPR and CCPA are driving companies to improve security and breach disclosure practices. However, as cybercrimes continue to evolve, businesses must go beyond just compliance and implement proactive cybersecurity strategies to stay ahead of emerging threats.
How companies can protect against data breaches
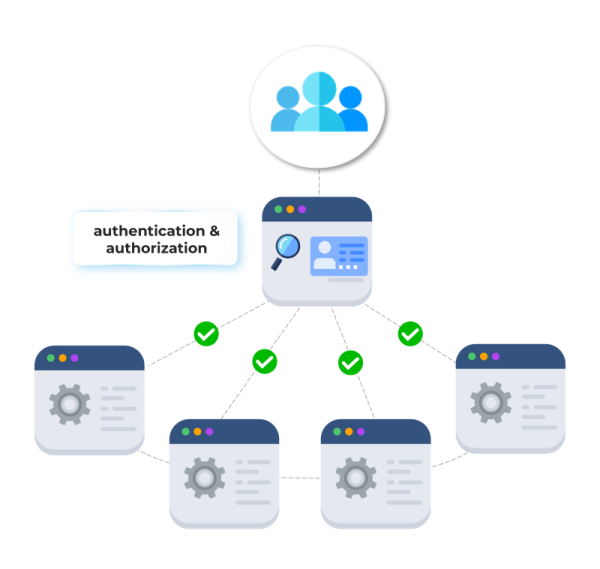
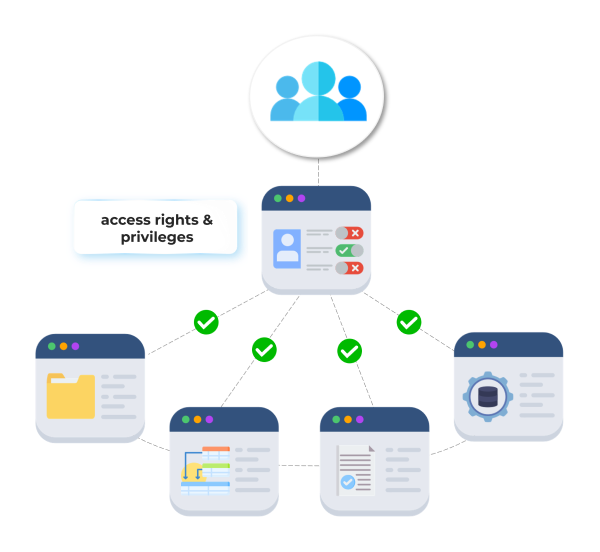
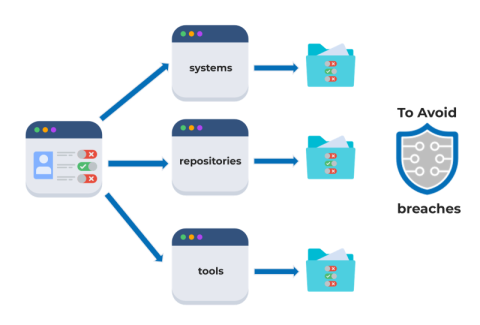
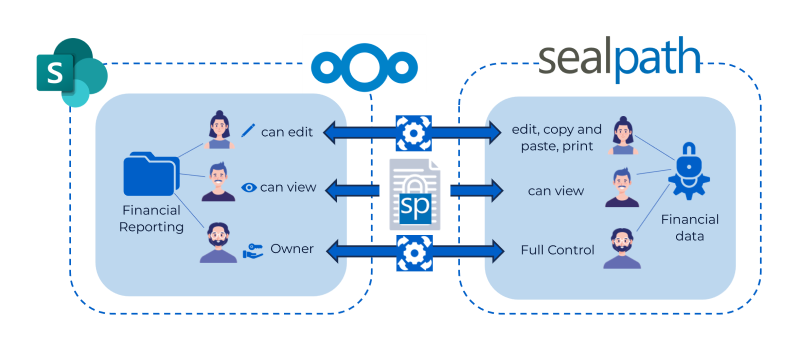
Cyberattacks are becoming more sophisticated, but businesses can take strategic steps to reduce the risk and minimize damage. Below are four essential measures every company should implement to strengthen cybersecurity and respond effectively to various data breach types.
Enforce strong access controls. Limiting access to sensitive data and systems with multi-factor authentication (MFA) and role-based permissions reduces the risk of insider threats and unauthorized intrusions. Regular
vulnerability management can help identify and address any weaknesses in these systems.
Keep systems updated and patched. Cybercriminals often exploit outdated software with known vulnerabilities. Regularly updating and patching applications, operating systems, and security tools can close these gaps and prevent attackers from using them as entry points.
Train employees to recognize cyber threats. Recent findings show that human error is the leading cause of data breaches[54]. Educating employees on phishing, social engineering, and secure data handling can reduce the likelihood of accidental leaks and security lapses. A well-trained staff acts as the first line of defense against cyber threats.
Monitor and contain breaches with threat detection tools. No system is completely immune to cyberattacks, which is why early detection is critical.
Data breach monitoring and threat detection and response solutions, like those provided by
NordStellar, can help businesses identify breaches in real time, contain the damage, and prevent attackers from spreading further within the network.
Additionally, the rise of
malware-as-a-service (MaaS) means companies must be prepared for increasingly accessible and powerful malware tools that may bypass traditional security measures. Rapid response and continuous monitoring can significantly reduce an incident’s impact.
References
[1] “ITRC sees third-most data breach victims in a quarter in Q2 2024,” Identity Theft Resource Center, Jul. 17, 2024. [Online]. Available: https://www.idtheftcenter.org/post/itrc-sees-third-most-data-breach-victims-in-quarter/
[2] “Breach information,” National Public Data, 2024. [Online]. Available: https://web.archive.org/web/20240813211719/https://nationalpublicdata.com/Breach.html
[3] Hofmann v. Jerico Pictures Inc., No. 024-CV-61383-SD (Fla. Aug. 1, 2024). Bloomberg Law. [Online]. Available: https://www.bloomberglaw.com/public/desktop/document/HofmannvJericoPicturesIncDocketNo024cv61383SDFlaAug012024CourtDoc?doc_id=X6S27DVM6H69DSQO6MTRAQRIVBS
[4] V. Petkauskas, “Billions of passwords and credentials leaked in the ‘Mother of All Breaches,'” Cybernews, Mar. 13, 2024. [Online]. Available: https://cybernews.com/security/billions-passwords-credentials-leaked-mother-of-all-breaches/
[5] “Cyber incident,” FBCS, Inc., n.d. [Online]. Available: https://www.fbcs-inc.com/cyber-incident/
[6] “Ticketmaster data security incident,” Ticketmaster, n.d. [Online]. Available: https://help.ticketmaster.com/hc/en-us/articles/26110487861137-Ticketmaster-Data-Security-Incident
[7] “Health data breach,” UnitedHealth Group. [Online]. Available: https://www.unitedhealthgroup.com/ns/health-data-breach.html
[8] “HIPAA substitute notice,” Change Healthcare. [Online]. Available: https://www.changehealthcare.com/hipaa-substitute-notice.html
[9] “Form 10-Q: Quarterly report,” US Securities and Exchange Commission. [Online]. Available: https://www.sec.gov/ix?doc=/Archives/edgar/data/0000732717/000073271724000046/t-20240506.htm
[10] “Addressing illegal download activity,” AT&T. [Online]. Available: https://about.att.com/story/2024/addressing-illegal-download.html
[11] D. Winder, “Dell confirms database hacked, hacker says 49 million customers hit,” Forbes, May 10, 2024. [Online]. Available: https://www.forbes.com/sites/daveywinder/2024/05/10/dell-confirms-database-hacked-hacker-says-49-million-customers-hit/
[12] “Threat actor claims sale of Dell database containing 49 million customer records,” Daily Dark Web, [Online]. Available: https://dailydarkweb.net/threat-actor-claims-sale-of-dell-database-containing-49-million-customer-records/
[13] “Update on cyber incident, 25 July 2024,” Synnovis. [Online]. Available: https://www.synnovis.co.uk/news-and-press/update-on-cyber-incident-25-july-2024
[14] “Cyberattack update, 01 July 2024,” Synnovis. [Online]. Available: https://www.synnovis.co.uk/news-and-press/cyberattack-update-01-july-2024
[15] “NHS London statement on Synnovis ransomware cyber attack,” NHS England, Jun. 4, 2024. [Online]. Available: https://www.england.nhs.uk/london/2024/06/04/nhs-london-statement-on-synnovis-ransomware-cyber-attack/
[16] “Synnovis ransomware cyber attack,” NHS England. [Online]. Available: https://www.england.nhs.uk/london/synnovis-ransomware-cyber-attack/
[17] “Cyber attack cost Synnovis an estimated £32.7m in 2024,” Digital Health, Jan. 2025. [Online]. Available: https://www.digitalhealth.net/2025/01/cyber-attack-cost-synnovis-estimated-32-7m-in-2024/
[18] “Update about an alleged incident regarding Twitter user data being sold online,” Twitter (X), 2023. [Online]. Available: https://privacy.x.com/en/blog/2023/update-about-an-alleged-incident-regarding-twitter-user-data-being-sold-online
[19] L. Abrams, “200 million Twitter users’ email addresses allegedly leaked online,” BleepingComputer, [Online]. Available: https://www.bleepingcomputer.com/news/security/200-million-twitter-users-email-addresses-allegedly-leaked-online/
[20] “MOVEit Transfer critical vulnerability,” Progress, May 31, 2023. [Online]. Available: https://community.progress.com/s/article/MOVEit-Transfer-Critical-Vulnerability-31May2023
[21] “MOVEit Transfer and MOVEit Cloud vulnerability,” Progress, [Online]. Available: https://www.progress.com/trust-center/moveit-transfer-and-moveit-cloud-vulnerability
[22] “MOVEit vulnerability,” National Cyber Security Centre, [Online]. Available: https://www.ncsc.gov.uk/information/moveit-vulnerability
[23] “Form 8-K: Current report,” US Securities and Exchange Commission, Aug. 6, 2024. [Online]. Available: [https://www.sec.gov/Archives/edgar/data/876167/000087616724000138/prgs-20240806.htm (https://www.sec.gov/Archives/edgar/data/876167/000087616724000138/prgs-20240806.htm)
[24] “MDL 3083: In Re: MOVEit Customer Data Security Breach Litigation,” US District Court for the District of Massachusetts, [Online]. Available: https://www.mad.uscourts.gov/caseinfo/multi-district-litigation.htm#:~:text=MDL%203083%3A%20In%20Re%3A%20MOVEit%20Customer%20Data%20Security%20Breach%20Litigation
[25] “Customer information,” T-Mobile, [Online]. Available: https://www.t-mobile.com/news/business/customer-information
[26] “Form 8-K: Current report,” US Securities and Exchange Commission, Jan. 9, 2023. [Online]. Available: https://www.sec.gov/ix?doc=/Archives/edgar/data/0001283699/000119312523010949/d641142d8k.htm
[27] “HCA Healthcare reports data security incident,” HCA Healthcare, [Online]. Available: https://investor.hcahealthcare.com/news/news-details/2023/HCA-Healthcare-Reports-Data-Security-Incident/default.aspx
[28] “Privacy update,” HCA Healthcare, [Online]. Available: https://hcahealthcare.com/about/privacy-update.dot
[29] “Form 8-K: Current report,” US Securities and Exchange Commission, Aug. 9, 2022. [Online]. Available: https://www.sec.gov/ix?doc=/Archives/edgar/data/0001512673/000119312522095215/d343042d8k.htm
[30] “Salinas, et al. v. Block, Inc. and Cash App Investing, LLC,” Cash App Security Settlement, [Online]. Available: https://cashappsecuritysettlement.com/home
[31] “An issue affecting some anonymous accounts,” X (Twitter), 2022. [Online]. Available: https://privacy.x.com/en/blog/2022/an-issue-affecting-some-anonymous-accounts
[32] L. Abrams, “Hacker selling Twitter account data of 54 million users for $30K,” BleepingComputer, [Online]. Available: https://www.bleepingcomputer.com/news/security/hacker-selling-twitter-account-data-of-54-million-users-for-30k/
[33] “Preliminary proxy statement,” US Securities and Exchange Commission, [Online]. Available: https://www.sec.gov/Archives/edgar/data/1839175/000119312521284329/d234831dprem14a.htm
[34] “Telecoms giant Syniverse discloses years-long data breach,” SecurityWeek, [Online]. Available: https://www.securityweek.com/telecoms-giant-syniverse-discloses-years-long-data-breach/
[35] A. Holmes, “Stolen data of 533 million Facebook users leaked online,” Business Insider, Apr. 3, 2021. [Online]. Available: https://www.businessinsider.com/stolen-data-of-533-million-facebook-users-leaked-online-2021-4?r=US&IR=T
[36] “Data Protection Commission announces decision in Facebook data scraping inquiry,” Data Protection Commission, [Online]. Available: https://www.dataprotection.ie/en/news-media/press-releases/data-protection-commission-announces-decision-in-facebook-data-scraping-inquiry
[37] Reuters, “Facebook users affected by data breach eligible for compensation, German court says,” Reuters, Nov. 18, 2024. [Online]. Available: https://www.reuters.com/technology/facebook-users-affected-by-data-breach-eligible-compensation-german-court-says-2024-11-18/
[38] P. Van Leemputten “Interne mail toont hoe Facebook veiligheidsproblemen wil ‘normaliseren,’” Data News, [Online]. Available: https://datanews.knack.be/nieuws/interne-mail-toont-hoe-facebook-veiligheidsproblemen-wil-normaliseren/
[39] D. Temple-Raston, “A worst nightmare cyberattack: The untold story of the SolarWinds hack,” NPR, Apr. 16, 2021. [Online]. Available: https://www.npr.org/2021/04/16/985439655/a-worst-nightmare-cyberattack-the-untold-story-of-the-solarwinds-hack
[40] “SolarWinds cyberattack demands significant federal and private sector response [infographic],” US Government Accountability Office, [Online]. Available: https://www.gao.gov/blog/solarwinds-cyberattack-demands-significant-federal-and-private-sector-response-infographic
[41] “Fact sheet: Imposing costs for harmful foreign activities by the Russian government,” The White House, Apr. 15, 2021. [Online]. Available: https://web.archive.org/web/20210422234636/https://www.whitehouse.gov/briefing-room/statements-releases/2021/04/15/fact-sheet-imposing-costs-for-harmful-foreign-activities-by-the-russian-government/
[42] “Press release 2024-174,” US Securities and Exchange Commission, [Online]. Available: https://www.sec.gov/newsroom/press-releases/2024-174
[43] C. Cimpanu, “Exclusive: Details of 10.6 million MGM hotel guests posted on a hacking forum,” ZDNet, [Online]. Available: https://www.zdnet.com/article/exclusive-details-of-10-6-million-of-mgm-hotel-guests-posted-on-a-hacking-forum/
[44] “Tonya Owens, et al. v. MGM Resorts International et al.,” US District Court for the District of Nevada, [Online]. Available: https://storage.courtlistener.com/recap/gov.uscourts.nvd.164564/gov.uscourts.nvd.164564.63.0.pdf
[45] “Marriott International notifies guests of property system incident,” Marriott International, Mar. 31, 2020. [Online]. Available: https://news.marriott.com/news/2020/03/31/marriott-international-notifies-guests-of-property-system-incident
[46] “Marriott International: Incident Notification,” Marriott International, [Online]. Available: https://web.archive.org/web/20200401163431/https://mysupport.marriott.com/
[47] “FTC takes action against Marriott, Starwood over multiple data breaches,” Federal Trade Commission, Oct. 2024. [Online]. Available: https://www.ftc.gov/news-events/news/press-releases/2024/10/ftc-takes-action-against-marriott-starwood-over-multiple-data-breaches
[48] “CAM4 responds to allegations of security breach,” CAM4, [Online]. Available: https://www.cam4.com/blog-uk/cam4-responds-to-allegations-of-security-breach/
[49] A. Bizga, “CAM4 data leak exposes personal data of millions of users,” Security Boulevard, May 2020. [Online]. Available: https://securityboulevard.com/2020/05/cam4-data-leak-exposes-personal-data-of-millions-of-users/
[50] A. M. Pitney, S. Penrod, M. Foraker, and S. Bhunia, “A systematic review of 2021 Microsoft Exchange data breach exploiting multiple vulnerabilities,” 2022 7th International Conference on Smart and Sustainable Technologies (SpliTech), Split / Bol, Croatia, 2022, pp. 1-6, https://doi.org/10.23919/SpliTech55088.2022.9854268
[51] “Active exploitation of Microsoft Exchange zero-day vulnerabilities,” Volexity, Mar. 2, 2021. [Online]. Available: https://www.volexity.com/blog/2021/03/02/active-exploitation-of-microsoft-exchange-zero-day-vulnerabilities/
[52] MSRC Team, “Multiple security updates released for Exchange Server,” Microsoft Security Response Center, Mar. 2021. [Online]. Available: https://msrc.microsoft.com/blog/2021/03/multiple-security-updates-released-for-exchange-server/
[53] 微博安全中心 (Weibo Security Center), “有关“微博用户信息被出售事件”的说明,” Weibo, [Online]. Available: https://weibo.com/2735327001/IzCMJioqC?from=page_1006062735327001_profile&wvr=6&mod=weibotime&type=comment
[54] “2024 Data Breach Investigations Report,” Verizon, 2024. [Online]. Available: https://www.verizon.com/business/resources/reports/dbir/?CMP=OOH_SMB_OTH_22222_MC_20200501_NA_NM20200079_00001
























:format(avif))
:format(avif))
:format(avif))
:format(avif))
:format(avif))
:format(avif))
:format(avif))